Inkjet-Printed Quantum Dot Fluorescent Security Labels with Triple-Level Optical Encryption | ACS Applied Materials & Interfaces

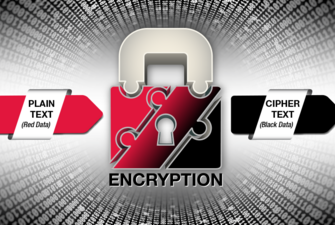
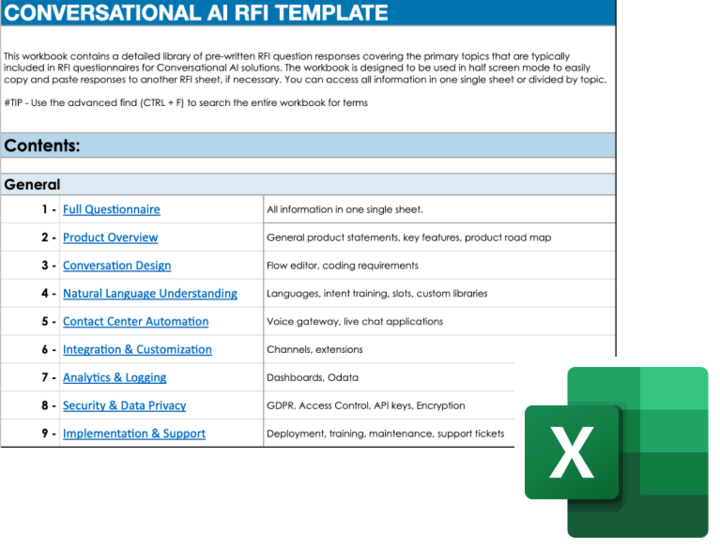
Electronics | Free Full-Text | Image Encryption Algorithm Combining Chaotic Image Encryption and Convolutional Neural Network

Boom Chicago Presents the 30 Most Important Years in Dutch History: Moskos, Andrew, Rosenfeld, Pep, Diehl, Matt, Maas, Saskia, Peele, Jordan, Meyers, Seth: 9781636141046: Amazon.com: Books

19 Security Awareness Statistics You Should Know Before Offering Training - Hashed Out by The SSL Store™

BlueSky Ransomware | AD Lateral Movement, Evasion and Fast Encryption Put Threat on the Radar - SentinelOne

Photo album Wehrmacht. German military photo album from the Second World War about soldiers of the Wehrmacht. Dark red artificial leather folder with a cord through the back. The interior consists of
/https://tf-cmsv2-smithsonianmag-media.s3.amazonaws.com/filer_public/4a/47/4a479f84-bbc6-44de-b055-215d1ad6d710/janfeb2023_n05_deadseascrolls.jpg)
How an Unorthodox Scholar Uses Technology to Expose Biblical Forgeries | History | Smithsonian Magazine

Official Publication Website InnoVEX is back, bringing the world's startups together on an all-new virtual platform

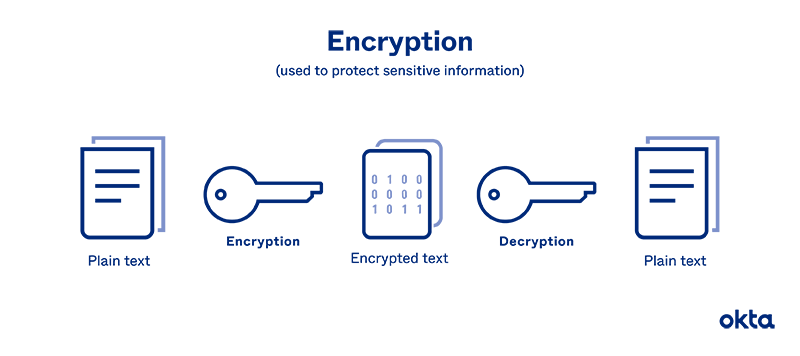
Preservation and Encryption in DNA Digital Data Storage - Zhang - 2022 - ChemPlusChem - Wiley Online Library